Introduction
Traditional perimeter-based security has become obsolete in today’s distributed digital landscape. With eighty-two percent of organizations operating in hybrid or multi-cloud infrastructures and remote work becoming the standard, the concept of a secure network boundary no longer exists.
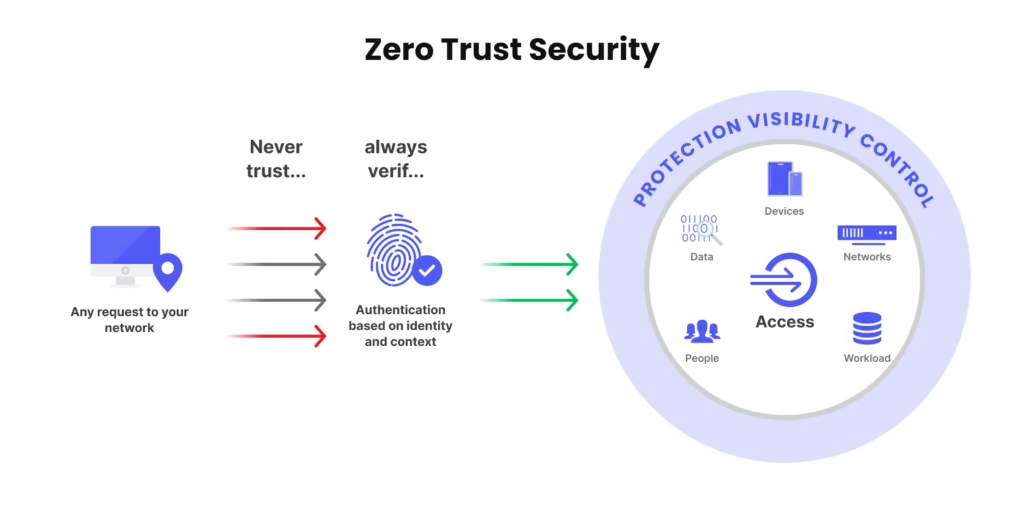
Zero trust security represents a fundamental paradigm shift in cybersecurity strategy. Rather than assuming everything inside a network perimeter is trustworthy, zero trust operates on a simple yet powerful principle: never trust, always verify. Every access request receives verification regardless of origin, and access is granted based on continuous authentication and contextual factors rather than simple network location.
Organizations implementing zero trust in 2026 have reported seventy-six percent fewer successful breaches and reduced incident response times from days to minutes, demonstrating the tangible business value of this approach. This comprehensive guide explores zero trust security architecture, implementation strategies, and best practices for building a robust security posture in 2026.
Understanding Zero Trust Architecture
The Core Principles
Zero trust architecture fundamentally reimagines how organizations approach security. Instead of establishing a defensive perimeter around networks and assuming everything inside is safe, zero trust treats every access attempt as potentially malicious.
The foundational principle is straightforward: never trust, always verify. This means continuous authentication and authorization for every user, device, application, and data flow regardless of whether connections originate from inside or outside traditional network boundaries.
A complementary principle is “assume breach.” Rather than trying to prevent every possible intrusion, zero trust assumes attackers have already gained access and implements controls that limit damage, prevent lateral movement, and detect malicious activities quickly.
The Shared Responsibility Model
Zero trust emphasizes continuous authentication and authorization of every user entity, device entity, and application, operating under the principles of never trust, always verify and assume breach. This approach proves critical for safeguarding sensitive data, systems, and services across modern distributed environments.
Organizations must understand that zero trust isn’t a product you can purchase or a one-time project you can complete. It represents a strategic approach to cybersecurity that continuously evolves with your environment, requiring ongoing commitment, adaptation, and refinement.
Moving Beyond Perimeter Security
The traditional castle-and-moat security model assumed threats existed primarily outside organizational networks. Once users or devices gained network access, they could move relatively freely within the perimeter.
This model fails catastrophically in modern environments where:
- Remote employees access corporate resources from home networks
- Cloud applications reside outside traditional perimeters
- Business partners and contractors require access to specific systems
- Mobile devices connect from diverse locations and networks
- Data flows constantly between on-premises and cloud environments
Zero trust replaces the binary “inside/outside” model with granular, identity-based access controls that verify every access request regardless of origin.
The Five Pillars of Zero Trust
Identity Verification and Access Management
Identity forms the foundation of zero trust architecture. Rather than trusting network locations, zero trust verifies user and device identities before granting access to any resource.
Implement strong authentication mechanisms including multi-factor authentication for all users, with particular emphasis on privileged accounts. Password-alone authentication proves insufficient against modern threats including phishing, credential stuffing, and social engineering attacks.
Identity federation allows users to access multiple systems with a single set of credentials while maintaining security. Single sign-on implementations simplify user experience while enabling centralized access control and monitoring.
Just-in-time access provisioning grants permissions only when needed and automatically revokes them after use. This time-based access control significantly reduces the window of opportunity for attackers and minimizes standing privileges that represent constant risk.
Privileged access management protects high-value credentials through secure vaults, session monitoring, and automated rotation. These controls prevent attackers from compromising administrative accounts that provide broad system access.
Device Security and Management
Every device accessing organizational resources must be verified, trusted, and continuously monitored. Device posture assessment evaluates security configurations, patch levels, and compliance status before allowing access.
Implement endpoint detection and response solutions that monitor device behavior continuously, identifying suspicious activities indicative of compromise. Mobile device management ensures corporate data remains protected even on employee-owned devices.
Device certificates provide cryptographic verification of device identity, preventing unauthorized or compromised devices from accessing sensitive resources. Regular device inventory and hygiene checks ensure only properly configured, up-to-date devices maintain access.
Network Segmentation and Micro-Segmentation
Network segmentation divides environments into isolated zones with strict controls governing traffic flow between segments. This limits an attacker’s ability to move laterally across your environment after initial compromise.
Micro-segmentation takes this concept further, implementing fine-grained controls at the workload level. Individual applications and services become isolated, preventing attackers from pivoting between systems even within the same network segment.
Software-defined perimeters create dynamic network boundaries based on identity and context rather than physical network topology. This approach proves particularly valuable for protecting cloud resources and supporting remote users.
Zero Trust Network Access solutions replace traditional VPNs by granting identity-based, per-application access instead of network-wide access. Applications remain invisible to unauthorized users, reducing exposure to external threats and preventing lateral movement.
Application and Workload Security
Secure applications throughout their entire lifecycle, from development through deployment and runtime operations. Integrate security controls into continuous integration and continuous deployment pipelines, identifying vulnerabilities early when they’re less expensive and disruptive to fix.
Implement application whitelisting that permits only approved software to execute. Container security features include image scanning for vulnerabilities, runtime monitoring for suspicious activities, and compliance enforcement for container configurations.
API security proves critical as applications increasingly communicate through application programming interfaces. Implement authentication, rate limiting, input validation, and comprehensive logging for all API endpoints.
Data Protection and Governance
Data represents the ultimate target for most attacks. Implement encryption for data at rest and in transit using strong cryptographic standards. Customer-managed encryption keys provide complete control over encryption key lifecycle management.
Data classification schemes categorize information based on sensitivity and regulatory requirements, enabling appropriate protection levels for different data types. Data loss prevention solutions monitor data movement, prevent unauthorized transfers, and enforce compliance with data handling policies.
Implement data access controls based on need-to-know principles, ensuring users can access only data required for their specific roles. Comprehensive audit logging tracks all data access and modifications, supporting forensic investigation and compliance reporting.
Implementation Strategy and Roadmap
Phase One: Assessment and Planning
Start by identifying your current exposure through assessing configurations, visibility gaps, and policy enforcement across identity, devices, and networks.
Conduct comprehensive inventory of all users, devices, applications, and data flows across your environment. Identify critical assets requiring the strongest protection and high-risk users who represent attractive targets for attackers.
Document existing security controls, identifying gaps between current state and zero trust requirements. This assessment provides the foundation for prioritizing implementation efforts.
Define clear objectives for your zero trust initiative, establishing measurable goals and success criteria. Secure executive sponsorship and budget for a multi-year transformation that requires sustained investment.
Phase Two: Quick Wins and Foundation Building
Begin implementation with focused use cases that demonstrate clear value while building foundational capabilities. Implement multi-factor authentication across all systems, starting with privileged accounts and gradually expanding coverage.
Deploy identity and access management platforms that provide single sign-on, centralized policy enforcement, and comprehensive access monitoring. Establish baseline security policies defining acceptable device configurations, required security software, and prohibited behaviors.
Implement network segmentation separating critical systems from general corporate networks. This foundational control limits potential breach impact while you develop more sophisticated capabilities.
Phase Three: Continuous Verification and Monitoring
Implement continuous authentication that validates user identity and device posture throughout sessions rather than just at initial login. Contextual access policies should evaluate risk factors including user behavior, access patterns, and requested resources.
Deploy security information and event management platforms that aggregate logs from across your environment, correlating events to identify sophisticated attack patterns. Enable comprehensive logging for all access attempts, policy decisions, and security events.
Implement user and entity behavior analytics that establish baselines for normal activity and alert on deviations. Machine learning-enhanced detection identifies subtle indicators of compromise that rule-based systems miss.
Phase Four: Automation and Orchestration
Leverage automation for policy enforcement to catch drift, monitor threat signals, and validate control effectiveness over time. Automated response capabilities can isolate compromised systems, revoke suspicious credentials, and block malicious traffic without waiting for human intervention.
Security orchestration platforms coordinate responses across diverse security tools, executing complex workflows automatically. This capability proves essential for matching the speed and sophistication of modern attacks.
Implement continuous configuration monitoring that detects drift from approved security standards. Automated remediation restores proper configurations before vulnerabilities become exploitable.
Phase Five: Maturity and Optimization
Continuously refine policies based on operational experience and evolving threats. Regular assessments evaluate control effectiveness, identifying areas requiring improvement or adjustment.
Expand zero trust implementation to previously unaddressed systems including operational technology, internet of things devices, and legacy applications that require specialized approaches.
Implement advanced capabilities including predictive analytics that anticipate attacks based on threat intelligence, behavioral anomalies, and vulnerability trends.
Technology Components and Tools
Zero Trust Network Access Solutions
ZTNA platforms provide secure access to applications without exposing them to the public internet or granting broad network access. Solutions verify user and device identity continuously, granting access only to specific applications rather than entire networks.
Leading ZTNA platforms integrate with identity providers, endpoint security tools, and security information systems to make contextual access decisions based on comprehensive risk assessment.
Identity and Access Management Platforms
IAM solutions authenticate users, manage identities, enforce access policies, and provide comprehensive audit trails. Modern platforms support diverse authentication methods including biometrics, hardware tokens, and risk-based adaptive authentication.
Identity governance capabilities automate access reviews, detect policy violations, and ensure least privilege principles through regular entitlement certification.
Cloud Security Posture Management
CSPM tools continuously monitor cloud configurations against security benchmarks, identifying misconfigurations before attackers exploit them. These platforms assess everything from overly permissive storage bucket settings to weak network access controls.
Automated remediation capabilities restore proper configurations, reducing the time between detection and resolution from days or hours to minutes.
Security Service Edge Solutions
Security Service Edge converges networking and security functions into unified cloud-delivered platforms. SSE includes secure web gateways, cloud access security brokers, and zero trust network access delivered as integrated services.
This convergence simplifies operations, reduces costs, and enables consistent policy enforcement regardless of where users connect or which applications they access.
AI-Enhanced Security Platforms
When zero trust is enhanced with artificial intelligence, the model becomes exponentially more effective, utilizing machine learning algorithms to identify patterns, predict threats, and automate responses at speeds impossible for human security teams.
AI-powered platforms analyze vast amounts of security telemetry, detecting sophisticated attack patterns and zero-day exploits that traditional signature-based systems miss. Behavioral analytics establish baselines for normal activity and identify anomalies indicating potential compromise.
Overcoming Implementation Challenges
Managing Complexity
Zero trust implementation touches virtually every aspect of IT operations, creating significant complexity. Organizations must coordinate changes across networks, applications, cloud services, identity systems, and endpoint management.
Address complexity through phased implementation that tackles manageable portions incrementally rather than attempting comprehensive transformation simultaneously. Establish clear governance structures defining roles, responsibilities, and decision-making authority.
Minimizing User Impact
Security changes can disrupt workflows, frustrate users, and reduce productivity if implemented poorly. Design zero trust implementations with user experience as a priority consideration.
Single sign-on reduces authentication friction while improving security. Risk-based authentication challenges users only when activities indicate elevated risk rather than requiring constant additional verification.
Communicate changes clearly to users, explaining why new requirements exist and how they protect both organizational and personal data. Provide comprehensive support during transitions, helping users adapt to new processes.
Integration with Legacy Systems
Many organizations operate legacy applications that lack modern authentication capabilities or cannot integrate with zero trust platforms. These systems require specialized approaches including application proxies, virtual patching, or compensating controls.
Prioritize modernization or replacement of legacy systems that represent significant security risks. For systems requiring continued operation, implement network segmentation and enhanced monitoring to mitigate risks.
Measuring Progress and Success
Zero trust isn’t a set-it-and-forget-it model, requiring ongoing validation to ensure your zero trust strategy keeps pace with reality, not just frameworks.
Establish key performance indicators measuring zero trust maturity including percentage of users with MFA enabled, percentage of applications protected by zero trust network access, mean time to detect anomalous activities, and policy compliance rates.
Regular assessments evaluate control effectiveness, identifying gaps and opportunities for improvement. Compare metrics against established baselines and industry benchmarks to validate progress.
Industry-Specific Considerations
Government and Defense
The Pentagon is preparing zero trust strategy 2.0, estimating it will be publicly available around March 2026, expanding implementation to operational technology, internet of things systems, defense critical infrastructure, and weapon systems.
Government agencies face strict compliance requirements and must protect highly sensitive information. Zero trust implementations must satisfy specific standards including NIST frameworks, Department of Defense requirements, and Federal Information Security Management Act regulations.
Healthcare Organizations
Healthcare environments include diverse devices, stringent privacy requirements, and 24/7 operational demands that complicate security implementations. Zero trust must protect electronic health records while enabling rapid access during emergencies.
Implement strong identity verification for healthcare providers, role-based access controls limiting data exposure, and comprehensive audit logging supporting HIPAA compliance.
Financial Services
Financial institutions face sophisticated threats, strict regulatory requirements, and customer expectations for seamless digital experiences. Zero trust implementations must balance security with user convenience.
Focus on transaction monitoring, fraud detection, and protecting customer financial data while enabling mobile banking and digital payment services.
Manufacturing and Critical Infrastructure
Manufacturing environments include operational technology systems that often lack security capabilities and cannot tolerate operational disruptions. Zero trust must protect intellectual property, product designs, and manufacturing processes.
Implement strong network segmentation isolating operational technology from IT networks, identity-based access for industrial control systems, and enhanced monitoring detecting unauthorized changes to critical configurations.
Best Practices for Zero Trust Success
Start with Identity
Build your zero trust implementation on a strong identity foundation. Consolidate identity systems, implement multi-factor authentication universally, and establish comprehensive identity governance before tackling other components.
Focus on High-Value Assets
Prioritize protection for your most critical systems and sensitive data. Implement strongest controls for crown jewels before addressing lower-risk resources.
Embrace Automation
Manual security processes cannot scale to match modern environment complexity or attack speed. Implement automation for policy enforcement, threat detection, and incident response.
Maintain Visibility
You cannot protect what you cannot see. Implement comprehensive logging and monitoring across all systems, providing security teams with the visibility necessary for effective threat detection and response.
Foster Security Culture
Technology alone cannot achieve zero trust. Develop security awareness throughout your organization, helping every employee understand their role in protecting data and systems.
Conclusion
Zero trust security represents the future of cybersecurity, providing adaptive, context-aware protection for modern distributed environments. While implementation requires significant effort and sustained commitment, the security benefits prove substantial.
Organizations embracing zero trust principles build resilient security postures capable of withstanding sophisticated attacks, supporting regulatory compliance, and enabling digital transformation initiatives. The journey toward zero trust is continuous, requiring ongoing refinement as threats evolve and environments change.
Begin your zero trust implementation today by assessing current security posture, identifying critical assets requiring protection, and developing a phased roadmap for transformation. The organizations that succeed will be those that commit to the journey, learn from experience, and continuously improve their security controls.
In 2026’s complex threat landscape, zero trust is no longer optional—it’s essential for protecting modern organizations against the sophisticated, persistent threats that define contemporary cybersecurity challenges.
Frequently Asked Questions
Q: What is zero trust security? A: Zero trust is a security model that eliminates implicit trust, requiring continuous verification of every user, device, and connection regardless of location. It operates on the principle “never trust, always verify.”
Q: How long does zero trust implementation take? A: Zero trust implementation typically spans multiple years, with initial capabilities deployed in 6-12 months and continuous maturity development over 3-5 years as organizations expand coverage and sophistication.
Q: Does zero trust replace firewalls and VPNs? A: Zero trust complements rather than completely replaces traditional security tools. It adds identity-based access controls and continuous verification while reducing reliance on perimeter-based security.
Q: What’s the difference between zero trust and VPN? A: VPNs grant network-level access based on successful authentication, while zero trust network access provides application-level access based on continuous identity verification and contextual risk assessment.
Q: How much does zero trust implementation cost? A: Costs vary widely based on organization size, existing infrastructure, and chosen solutions, typically ranging from tens of thousands for small businesses to millions for large enterprises.
Q: Can small businesses implement zero trust? A: Yes. Cloud-based security services and managed security providers make zero trust capabilities accessible to organizations of all sizes without requiring massive internal security teams.
Q: What are the main challenges in zero trust implementation? A: Key challenges include managing complexity across diverse systems, integrating with legacy applications, minimizing user disruption, and maintaining ongoing commitment over multi-year implementations.
Q: How does AI enhance zero trust security? A: AI enables behavioral analytics, predictive threat detection, and automated response at machine speed, identifying sophisticated attacks that rule-based systems miss while reducing analyst workload.