Introduction
Data breaches have become one of the most devastating threats facing organizations in 2026. With the average cost of a data breach reaching four point four four million dollars, businesses cannot afford to treat data security as an afterthought. Recent statistics reveal that one in three enterprises experienced a breach in the preceding twelve months, highlighting the urgent need for comprehensive data breach prevention strategies.
The landscape of cyber threats has evolved dramatically. Attackers now leverage artificial intelligence to execute sophisticated campaigns, exploit third-party vulnerabilities, and bypass traditional security controls at unprecedented speed. According to recent industry research, external attackers cause sixty-seven percent of breaches, while eighty-one percent involve weak or stolen passwords.
However, the situation isn’t hopeless. Organizations implementing proactive data breach prevention measures successfully protect sensitive information while maintaining business operations. This comprehensive guide explores ten powerful strategies that combine technology, processes, and people to create robust defense against modern threats. Whether you’re a small business or large enterprise, these proven techniques will help you secure your data and protect your reputation in 2026.
Understanding Data Breach Prevention
What Makes Data Breach Prevention Critical
Data breach prevention focuses on stopping unauthorized access to sensitive information before exposure occurs. Unlike reactive approaches that respond after incidents, prevention strategies address vulnerabilities proactively, reducing the likelihood of successful attacks.
Research shows that breaches taking more than two hundred days to detect and contain cost an average of five point zero one million dollars. Organizations with strong data breach prevention programs detect threats in under one hundred days, reducing costs by approximately one point one million dollars. This demonstrates that prevention isn’t just about security—it’s sound financial strategy.
The True Cost of Data Breaches
Beyond immediate financial impact, data breaches cause lasting damage including regulatory fines and penalties that can reach millions, loss of customer trust leading to revenue decline, legal fees from class action lawsuits, operational disruption during investigation and recovery, competitive disadvantage from stolen intellectual property, and increased insurance premiums.
Healthcare breaches remain the most expensive, averaging seven point four two million dollars per incident. Healthcare has held this dubious distinction for twelve consecutive years, emphasizing the critical importance of data breach prevention in regulated industries.
10 Powerful Data Breach Prevention Strategies
1. Implement Comprehensive Data Discovery and Classification
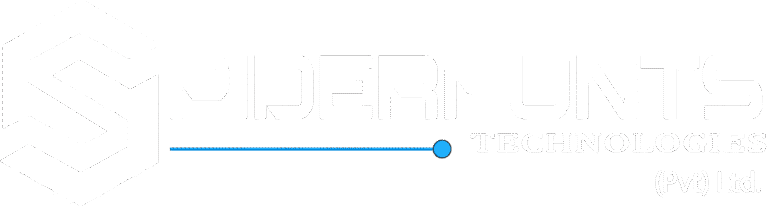
Show Image Alt text: Data breach prevention starts with comprehensive data classification and discovery processes
Effective data breach prevention begins with understanding what data you have and where it resides. Many organizations cannot answer basic questions about their data landscape, creating blind spots that attackers exploit.
Conduct thorough data discovery across all systems, identifying every location where sensitive information is stored, processed, or transmitted. This includes on-premises servers, cloud environments, employee devices, and third-party systems.
Implement data classification schemes categorizing information based on sensitivity levels such as public information requiring no special protection, internal data for employees only, confidential information with restricted access, and highly sensitive data demanding strongest controls.
Automated classification tools scan files, databases, and communications, applying appropriate labels based on content. This enables consistent policy enforcement regardless of where data moves within your organization.
Link to our comprehensive data classification guide for detailed implementation steps.
2. Enforce Strong Access Controls and Least Privilege
Show Image Alt text: Data breach prevention through role-based access controls and least privilege implementation
Access control represents one of the most effective data breach prevention techniques. Research indicates that eighty-one percent of breaches involve compromised credentials, making identity and access management critical.
Implement the principle of least privilege, granting users minimum permissions necessary for their roles. Regular access reviews identify and remove unnecessary permissions that accumulate over time.
Privileged access management solutions protect high-value administrative credentials through secure vaults, just-in-time provisioning that grants elevated access only when needed, session recording for accountability, and automatic credential rotation.
Multi-factor authentication adds essential protection layers. Enable MFA universally, with particular emphasis on privileged accounts, remote access, and systems handling sensitive data.
Visit NIST’s access control guidelines for industry best practices.
3. Deploy AI-Enhanced Threat Detection Systems
Show Image Alt text: Data breach prevention using artificial intelligence and machine learning for threat detection
Traditional signature-based security cannot keep pace with modern threats. Organizations require AI-enhanced detection systems analyzing behavioral patterns and identifying anomalies invisible to human analysts.
Security Information and Event Management platforms aggregate logs from across environments, correlating events to detect sophisticated attack patterns. Machine learning models establish baselines for normal activity, alerting on deviations that indicate potential breaches.
User and Entity Behavior Analytics monitor how employees and systems interact with data. Unusual access patterns, unexpected data transfers, or suspicious authentication attempts trigger immediate investigation.
Predictive analytics anticipate attacks based on threat intelligence, vulnerability trends, and historical patterns. This enables proactive data breach prevention by addressing threats before they materialize.
Explore CISA’s detection resources for implementation guidance.
4. Strengthen Data Breach Prevention Through Encryption
Show Image Alt text: Data breach prevention strategy showing end-to-end encryption for sensitive information
Encryption provides essential protection ensuring that even if attackers access data, they cannot read it without decryption keys. Implement encryption for data at rest protecting stored information on servers and devices, data in transit securing information moving across networks, and data in use safeguarding information during processing.
Use strong encryption standards including AES-256 for symmetric encryption and RSA-4096 or elliptic curve cryptography for asymmetric encryption. Customer-managed encryption keys provide complete control over key lifecycle management.
Proper key management proves as critical as encryption itself. Store keys separately from encrypted data, implement regular key rotation schedules, maintain comprehensive audit logs, and establish clear key recovery procedures.
With quantum computing threats emerging, begin planning migration to post-quantum cryptography. Organizations have finite windows to inventory cryptographic dependencies and transition to quantum-resistant algorithms.
Learn more about encryption best practices from NIST’s cryptography resources.
5. Build Comprehensive Security Awareness Training Programs
Show Image Alt text: Data breach prevention through employee security awareness and phishing simulation training
Human error contributes to seventy-four percent of successful breaches, making employee training essential for data breach prevention. However, annual compliance training proves insufficient against sophisticated social engineering.
Implement continuous education programs including monthly security updates, simulated phishing campaigns testing employee vigilance, interactive scenarios demonstrating real-world threats, role-specific training addressing unique risks, and gamification increasing engagement.
Training should specifically address recognizing phishing attempts, protecting credentials, handling sensitive data properly, reporting security incidents, and identifying social engineering tactics.
Measure training effectiveness through metrics like phishing simulation click rates, security incident reporting frequency, and time to report suspicious activities. Adjust programs based on performance data.
Consult SANS Security Awareness for proven training frameworks.
6. Implement Robust Vulnerability Management for Data Breach Prevention
Show Image Alt text: Data breach prevention through continuous vulnerability scanning and rapid patch deployment
Unpatched vulnerabilities provide easy entry points for attackers. Organizations must prioritize rapid identification and remediation of security weaknesses.
Continuous vulnerability scanning assesses infrastructure, applications, and systems for known vulnerabilities. Automated tools provide real-time visibility into security posture changes as new systems deploy or threats emerge.
Risk-based prioritization focuses remediation efforts on vulnerabilities most likely to be exploited. Consider factors including exploit availability, system exposure, data sensitivity, and business criticality.
Automated patch management systems test and deploy security updates rapidly. Establish clear patch management policies defining maximum time-to-patch for different severity levels.
For systems that cannot receive immediate patching, implement compensating controls including network segmentation, enhanced monitoring, virtual patching, or access restrictions.
Reference CVE database for vulnerability tracking and NVD for severity ratings.
7. Secure Third-Party Relationships and Supply Chains
Show Image Alt text: Data breach prevention through vendor security assessments and supply chain risk management
Third-party involvement in breaches doubled to thirty percent, making vendor security critical for data breach prevention. Your security posture is only as strong as your weakest third-party relationship.
Conduct thorough due diligence before granting vendor access. Review security certifications, assess security practices, verify compliance with relevant standards, and evaluate incident response capabilities.
Implement strict vendor access controls limiting permissions to specific systems and data, requiring multi-factor authentication, monitoring vendor activities continuously, and automatically expiring access credentials.
Contractual requirements should mandate security standards, require breach notifications, establish liability for security failures, and permit security audits.
Regular vendor assessments ensure ongoing compliance with security requirements. High-risk vendors require more frequent evaluation and monitoring.
Visit NIST’s supply chain guidance for comprehensive frameworks.
8. Deploy Endpoint Protection and Data Loss Prevention
Show Image Alt text: Data breach prevention using endpoint detection response and data loss prevention technologies
Endpoints represent primary attack surfaces in distributed work environments. Comprehensive endpoint protection proves essential for data breach prevention.
Endpoint Detection and Response solutions monitor device behavior continuously, identifying malicious activities, providing automated response capabilities, and enabling forensic investigation. EDR detects ransomware, credential theft, and lateral movement attempts.
Data Loss Prevention monitors data movement across endpoints, preventing unauthorized transfers to external drives, cloud storage, email, or messaging applications. DLP enforces policies based on data classification, user roles, and business requirements.
Mobile Device Management secures smartphones and tablets accessing corporate data. MDM enables remote wiping, enforces security configurations, and separates corporate data from personal information.
Explore Endpoint Security best practices from CISA.
9. Establish Comprehensive Backup and Recovery Procedures
Show Image Alt text: Data breach prevention and recovery through comprehensive backup systems and procedures
While backups don’t prevent breaches directly, they prove essential for data breach prevention strategies by enabling recovery without paying ransoms or accepting data loss.
Implement the three-two-one backup rule maintaining three copies of data on two different media types with one copy stored offline or offsite. Immutable backups that cannot be modified protect against ransomware targeting backup systems.
Test restoration procedures regularly ensuring backups contain recoverable data and teams can execute restoration efficiently. Many organizations discover during actual incidents that backups are incomplete or corrupted.
Segregate backup infrastructure from production networks preventing attackers from compromising both simultaneously. Implement strict access controls limiting who can access or modify backups.
10. Develop and Test Incident Response Plans
Show Image Alt text: Data breach prevention includes comprehensive incident response planning and regular testing
Despite best data breach prevention efforts, incidents occasionally occur. Comprehensive incident response plans minimize damage when breaches happen.
Incident response plans should define roles and responsibilities, establish communication protocols, outline technical response procedures, specify decision-making authority, and include notification requirements for regulators and affected parties.
Practice incident response through tabletop exercises and simulated breaches. These exercises reveal gaps in procedures, clarify responsibilities, and build response capabilities.
Post-incident analysis identifies how attacks succeeded and what improvements prevent recurrence. Document lessons learned and implement changes promptly.
Review NIST’s incident response guide for detailed frameworks.
Measuring Data Breach Prevention Success
Organizations must track key performance indicators demonstrating data breach prevention program effectiveness. Important metrics include mean time to detect threats, mean time to respond to incidents, number of detected vulnerabilities, patch deployment timeframes, security awareness training completion rates, and phishing simulation click rates.
Compare performance against established baselines and industry benchmarks. Demonstrate improvement over time, justifying continued security investments to leadership.
External validation through security assessments, penetration testing, and compliance audits provides objective evaluation of your data breach prevention posture.
Industry-Specific Data Breach Prevention Considerations
Healthcare organizations must protect electronic health records while maintaining HIPAA compliance and enabling rapid access during emergencies. Implement role-based controls, comprehensive audit logging, and encryption for protected health information.
Financial services face sophisticated threats targeting high-value transactions. Deploy transaction monitoring, fraud detection, and multi-channel verification for significant financial movements.
Manufacturing environments require operational technology security protecting intellectual property and production systems. Implement network segmentation isolating OT from IT systems.
Small businesses often lack dedicated security teams but remain attractive targets. Focus on fundamental controls including automated backups, multi-factor authentication, email security, and employee training. Consider managed security services providing enterprise-grade protection.
Conclusion
Data breach prevention in 2026 requires comprehensive strategies addressing technology, processes, and people. While attack sophistication continues increasing, organizations implementing robust defenses successfully protect sensitive information and maintain stakeholder trust.
Success demands moving beyond reactive approaches to proactive data breach prevention combining AI-enhanced detection, strong access controls, encryption, security awareness training, vulnerability management, third-party risk management, endpoint protection, backup systems, and incident response planning.
The strategies outlined in this guide provide actionable roadmaps for building resilient data breach prevention programs. Organizations that invest in these proven techniques will be best positioned to defend against modern threats while supporting business growth and digital transformation initiatives.
Remember that data breach prevention represents ongoing operations rather than one-time projects. Continuous improvement, adaptation to emerging threats, and sustained commitment prove essential for long-term security success.
Frequently Asked Questions
Q: What is data breach prevention? A: Data breach prevention focuses on stopping unauthorized access to sensitive information before exposure occurs through proactive security controls, vulnerability management, access restrictions, and continuous monitoring.
Q: How much does the average data breach cost in 2026? A: The global average cost of a data breach in 2026 is four point four four million dollars, with healthcare breaches averaging seven point four two million dollars per incident.
Q: What causes most data breaches? A: External attackers cause sixty-seven percent of breaches, with phishing involved in forty-four percent of incidents. Eighty-one percent of breaches involve weak or stolen passwords.
Q: How long does it take to detect a data breach? A: On average, it takes one hundred ninety-four days to identify a breach and sixty-four days to contain it. Organizations with strong prevention programs detect breaches significantly faster.
Q: Can small businesses afford effective data breach prevention? A: Yes. Cloud-based security services and managed security providers make enterprise-grade data breach prevention accessible to organizations of all sizes without requiring large internal teams.
Q: What role does employee training play in data breach prevention? A: Critical. Human error contributes to seventy-four percent of successful breaches, making security awareness training essential for effective data breach prevention programs.
Q: How often should data breach prevention measures be updated? A: Continuously. Threats evolve constantly, requiring ongoing assessment, adaptation, and improvement of data breach prevention controls and procedures.
Q: What industries face the highest data breach risks? A: Healthcare, financial services, retail, and technology sectors face elevated risks due to valuable data, regulatory requirements, and attractive targets for cybercriminals.